Modern case management for security investigations
Collaborate on malware infections, phishing emails, IDS alerts, insider abuse, and everything else.
How it works
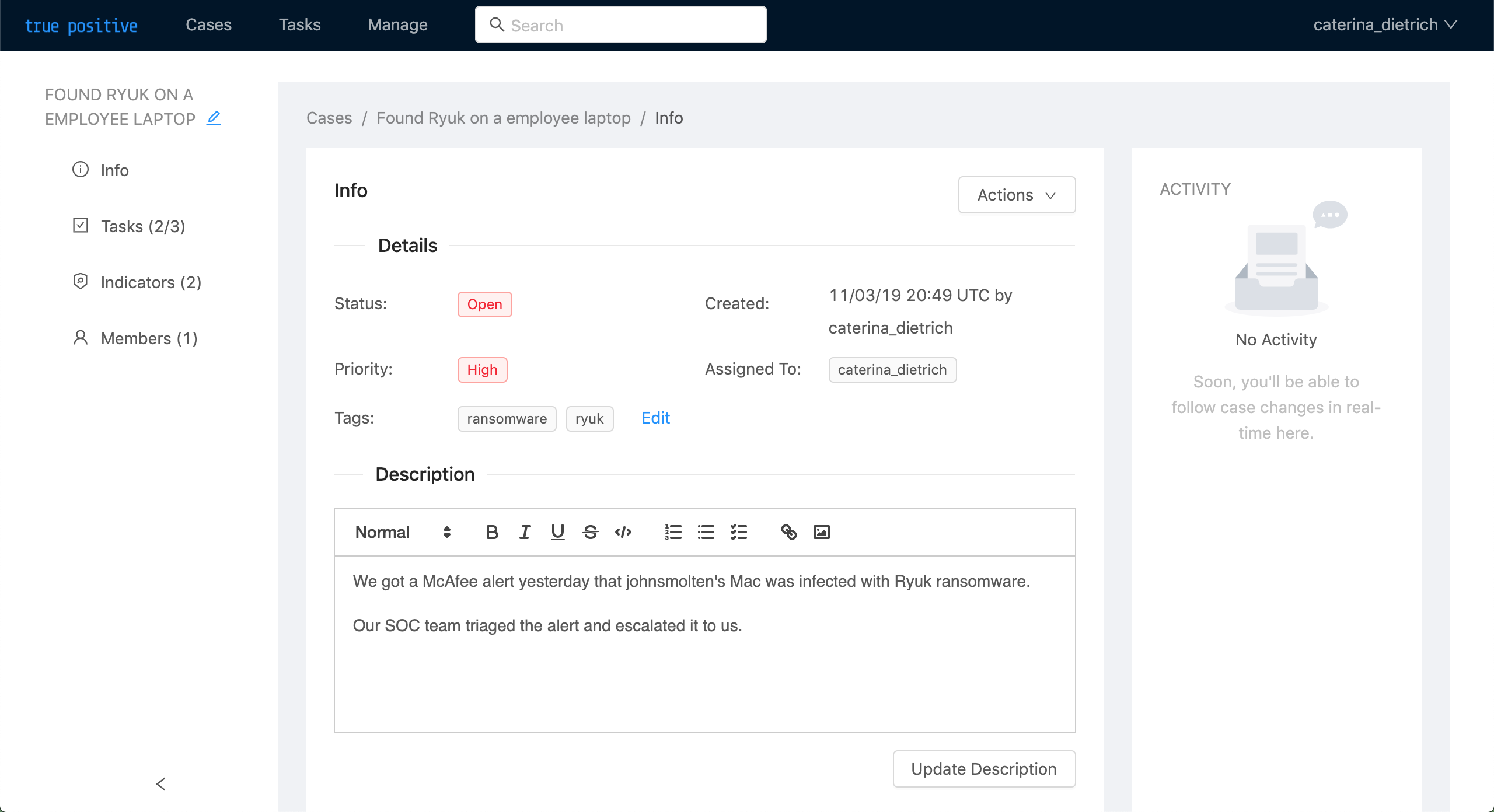
1. Create a case
A case collects all the information about an investigation.
2. Add tasks
Divide work to complete into tasks, which you can assign and comment on.
3. Add indicators
Add indicators of compromise like IP addresses, domains, URLs, and file hashes to your case.
Standardize your organization's incident handling
1. Create task templates
Define a task template for each task to add to your case template.
This way, you can add the same task to multiple case templates.
2. Create a case template
You can add, group, and reorder task templates in your case template.
3. Create a case from your template
It only takes one click.
Features
Customize statuses and priorities
Edit the default set of case statuses and priorities to fit your org's workflow.
Create cases from email
Easily create cases from emails sent to a corporate mailbox, like phishing@company.com.
Just generate a inbound address in the UI and forward emails from your mailbox to the inbound address.
Restrict access to cases
Only users and groups who are members of a group can access it.
You can grant either edit or view access to a case.
GraphQL API
Everything you can do in the web console, you can do in our API. The console uses the same API that we expose to customers.
We also have an interactive API playground.
Merge Cases
Merge a case into another if you realize it's a duplicate.
You can merge as many cases as you'd like into a case, and merging a case doesn't modify it at all.